Cloud SIEM As a Service
Fortify Your Software with Expert Secure Code Reviews.!!!
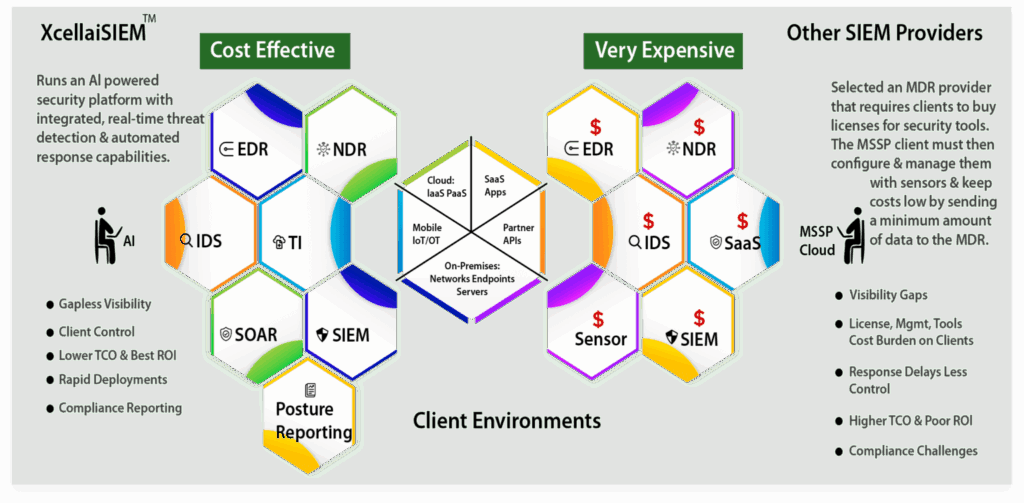
Platform built grounds up with DTM, ML & Al to analyze all telemetry in single context with situational awareness to Proactively Detect & Auto/Playbook based Elimination/Containment of Threats & Breaches.
Product Intro
Use Cases
Get real time contextual security visibility
Platform built grounds up with DTM, ML & Al to analyze all telemetry in single context with situational awareness to Proactively Detect & Auto Playbook based Elimination Containment of Threats & Breaches.

Featured Use Cases?
Powerful Cloud Features
Advanced Threat Detection
Continuously monitors endpoints
Malware Detection
A critical cybersecurity process involving
Ransomware Detection
the process of identifying malicious
Vulnerability Exploits
Vulnerability exploits are techniques, tools,
Security information
Approach to security management
Security operations center
organization's threat detection,
Monitoring network traffic
for suspicious patterns
Detecting malicious activities
Activities within a network.

